Stop drowning in vulnerability noise. Start managing exposure strategically.
Thousands of ‘critical’ alerts. Limited resources. No clear way to prioritise. Your security team knows the tools aren’t the problem—the decisions are.
Orro’s Continuous Threat Exposure Management (CTEM) service helps Australian organisations move from reactive vulnerability management to strategic exposure control—using context, not just severity, to prioritise what actually threatens your business.
If this sounds familiar, you’re not alone
Security teams across Australia are facing the same challenge: more visibility than ever before, but less clarity about what to do with it. The volume of vulnerability data has exploded, but the ability to make confident decisions hasn’t kept pace.
 Pain Point 1: Flooded with “Critical”
Pain Point 1: Flooded with “Critical”
“We have 5,000 critical vulnerabilities. We fix 100, and tomorrow there are 5,000 more.”
Your vulnerability scanner doesn’t lie—but it doesn’t prioritise either. When everything carries a CVSS score above 8.0, everything is labelled “critical.” Your team is stuck in an endless cycle of patching without measurably reducing real risk. According to recent industry research, organisations process an average of 960 security alerts per day, with large enterprises handling over 3,000 daily alerts—yet fewer than 5% require immediate action. The rest is noise—but noise that costs time, money, and analyst morale.
Business impact: Burnout. Wasted resources. No measurable improvement in security posture despite heroic effort.
 Pain Point 2: Lack of Business Context
Pain Point 2: Lack of Business Context
“Our scanner tells us a server has a vulnerability, but it doesn’t know that server holds our most sensitive customer data.”
Traditional vulnerability management treats all assets equally. A CVSS 9.8 vulnerability on an isolated test server receives the same “critical” rating as the same vulnerability on your internet-facing customer database. But these represent fundamentally different levels of business risk. Without context about asset criticality, network position, and data sensitivity, you’re fixing vulnerabilities in the order your scanner finds them—not in the order that actually reduces business risk.
Business impact: You’re remediating the wrong things first, leaving the exposures that genuinely threaten business continuity unaddressed while exhausting resources on low-impact items.
 Pain Point 3: Unknown Attack Surface
Pain Point 3: Unknown Attack Surface
“We only scan what we know about. We’re worried about what we don’t see.”
Shadow IT. Forgotten cloud instances. Orphaned containers from last year’s project. Employee-spun AWS environments. Your attack surface is growing faster than your inventory can track. Traditional vulnerability scanning operates on a fundamental assumption: you know what assets exist to scan. But in modern hybrid environments—on-premise infrastructure, multiple cloud platforms, SaaS applications, and operational technology—this assumption breaks down. Research from [SOURCE NEEDED: Cloud Security Alliance or similar] indicates that the average enterprise has visibility into only 60-70% of their actual cloud assets.
Business impact: Unknown exposure equals unmanaged risk. And attackers are exceptionally good at finding the blind spots.
 Pain Point 4: Security vs Operations Tension
Pain Point 4: Security vs Operations Tension
“IT Operations pushes back on patching because they don’t believe the risk is real.”
Security says “critical,” Operations says “prove it.” Without business context, every vulnerability conversation becomes a negotiation. Security teams can’t articulate why this particular patch matters more than the 4,000 others in the queue. Operations teams, rightly concerned about stability and uptime, demand justification before disrupting production systems. The result: critical remediations get delayed, relationships deteriorate, and actual risk remains unaddressed.
Business impact: Adversarial internal relationships, slow remediation cycles, and compromises that leave genuine business risks unpatched.
The problem isn’t visibility. It’s decision-making.
Most organisations have more security data than ever before. Multiple vulnerability scanners. Thousands of log sources. Dozens of dashboards. Security Information and Event Management (SIEM) platforms processing millions of events daily. Cloud security posture management tools monitoring infrastructure changes. Endpoint Detection and Response (EDR) agents on every device.
But all this visibility hasn’t made decisions easier—it’s made them harder.
Because knowing about a vulnerability isn’t the same as knowing what to do about it.
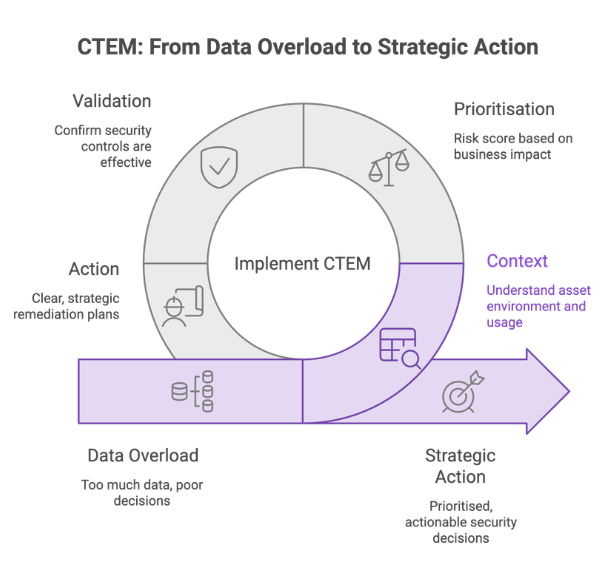
This is the fundamental insight behind why Continuous Threat Exposure Management (CTEM) is emerging as the next evolution in cybersecurity. Coined by Gartner in their research on modern security operations, CTEM represents a shift from vulnerability-centric thinking to exposure-centric thinking—from asking “what’s broken?” to asking “what’s actually threatening our business?”
What CTEM Actually Means
CTEM doesn’t replace your existing security tools. It adds the missing layer: context, prioritisation, and strategic action.
Where traditional vulnerability management provides you with a list of technical findings, CTEM provides you with a risk-prioritised action plan. It answers the questions security leaders actually need answered:
- Which of these 5,000 vulnerabilities can actually be exploited in our environment?
- Which exposures threaten our most critical business operations?
- Are our existing security controls effectively blocking the attack paths that matter?
- What should we fix first to achieve the greatest risk reduction?
- How do we demonstrate to the board that our security posture is improving?
The Four Pillars of CTEM
- CONTEXT
Understanding where assets sit in your environment, what they’re used for, who has access, and whether attack paths are actually exploitable. A critical vulnerability on an internet-facing production database demands different urgency than the same vulnerability on an isolated development server with no sensitive data. - PRIORITISATION
Risk scoring based on business impact and exploitability, not just CVSS severity. This means factoring in threat intelligence (is this being actively exploited?), asset criticality (does this system process customer data?), and network position (is this externally accessible?). - VALIDATION
Confirming that your security controls are actually working. Just because you have a Web Application Firewall (WAF) doesn’t mean it’s blocking the attacks that matter. CTEM validates control effectiveness by testing whether attack paths are genuinely mitigated. - ACTION
Clear, strategic remediation plans—not 200-page reports to interpret. You need to know exactly what to patch, what to reconfigure, what to isolate, and what to rebuild. And you need this guidance in language that Operations teams can act on and executives can understand.
How Orro makes exposure management work in practice
Orro’s approach to Continuous Threat Exposure Management is built on nearly 30 years of Australian cybersecurity expertise. Operating from our National Cyber Defence Centre, our security analysts monitor millions of events daily for organisations across financial services, government, healthcare, and critical infrastructure. We’ve seen firsthand why traditional vulnerability management fails—and we’ve built our CTEM service to solve exactly those problems.
Context Over Severity
We don’t rely solely on CVSS scores.
Instead, we calculate risk based on multiple contextual factors:
Asset Context
– Where does this asset sit in your network architecture? – What business function does it serve? – What data does it process or store? – Who has access to it? – Is it internet-facing or internal-only?
Threat Intelligence
– Is this vulnerability being actively exploited in the wild right now? – Have we seen exploitation attempts in our threat intelligence feeds? – Is there public exploit code available? – What’s the actual exploitability in real-world conditions?
Compensating Controls
– Are there security controls that would block this attack path? – Is there a Web Application Firewall protecting this application? – Are network segmentation policies preventing lateral movement? – Would endpoint detection catch an exploitation attempt?
The result: A CVSS 9.8 vulnerability on an isolated test server with no sensitive data gets appropriately deprioritised. A CVSS 6.5 vulnerability on your internet-facing customer portal with no compensating controls moves to the top of the remediation queue.
This “context over severity” approach is what transforms vulnerability data into genuine risk intelligence.
Integration, Not Replacement
We work with your existing security investments.
One of the most common objections we hear: “We already have vulnerability scanning tools. We don’t want to rip and replace what’s working.”
Good news: you don’t have to.
Orro’s CTEM service, built on the Rapid7 Command platform, integrates with 100+ existing security tools:
- Vulnerability Management: Rapid7, Qualys, Tenable, Microsoft Defender for Vulnerability Management
- Endpoint Detection & Response: SentinelOne, CrowdStrike, Microsoft Defender for Endpoint
- Cloud Security: AWS Security Hub, Azure Security Center, Google Cloud Security Command Center
- Network & Infrastructure: Network scanning tools, asset discovery platforms
- Identity & Access: Azure AD, Okta, Active Directory security assessments
Our platform consolidates data from across your security ecosystem into a single, contextualised risk view. You keep the tools you’ve invested in—we make them work together to give you decision-ready intelligence instead of disconnected findings.
Actionable Remediation, Not Generic PDFs
You don’t get a 200-page report to interpret.
You get clear, prioritised actions:
Top 10-20 Exposures
The specific vulnerabilities and misconfigurations that genuinely threaten business continuity, ranked by actual risk—not theoretical severity.
Specific Remediation Steps
Not “patch CVE-2024-1234.” Instead: “Patch the customer authentication service running on servers PROD-WEB-01 through PROD-WEB-04. This is internet-facing, processes customer credentials, and has active exploitation in the wild. IT Operations contact: [name]. Estimated downtime: 15 minutes. Remediation priority: This week.”
Business Justification
Every high-priority remediation includes context for why this matters: “This vulnerability allows unauthenticated remote code execution on your customer-facing web application. Successful exploitation could result in customer data breach, regulatory notification requirements under the Privacy Act, and significant reputational damage.”
Control Validation Findings
Where your existing security controls are working (so you can avoid wasted effort) and where they’re not (so you know where exposure remains despite controls).
This level of specificity transforms security findings from technical documentation into operational action plans.
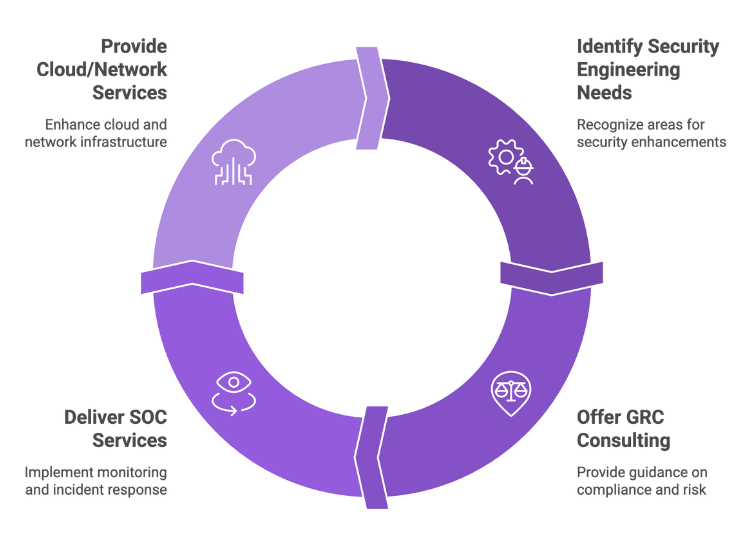
Strategic Consulting, Not Just Tooling
CTEM findings naturally inform broader security strategy.
As we work with organisations to understand and manage their exposure, patterns emerge that go beyond individual vulnerabilities:
Security Architecture Gaps
“Your external attack surface analysis reveals 15 internet-facing services that IT Operations wasn’t aware existed. This suggests a broader shadow IT governance challenge that requires policy and architecture work, not just patching.”
Control Effectiveness Issues
“We’ve validated your Web Application Firewall configuration and found it’s blocking only 40% of the attack categories it should prevent. You need security engineering support to reconfigure these rules properly.”
GRC & Policy Updates
“Your exposure assessment shows that 60% of your highest-risk findings relate to insecure identity and access configurations—misaligned with your documented security baseline policies. Your GRC function needs to update these policies to reflect current best practices.”
SOC Monitoring Priorities
“Based on validated threat paths that can’t be immediately remediated, here are the specific attack patterns your SOC should be monitoring for. This isn’t theoretical—these are the genuine risks in your environment.”
This strategic consulting approach is what differentiates Orro from vendors who simply sell you a platform and walk away. We’re invested in your security outcomes, not just tool deployment.
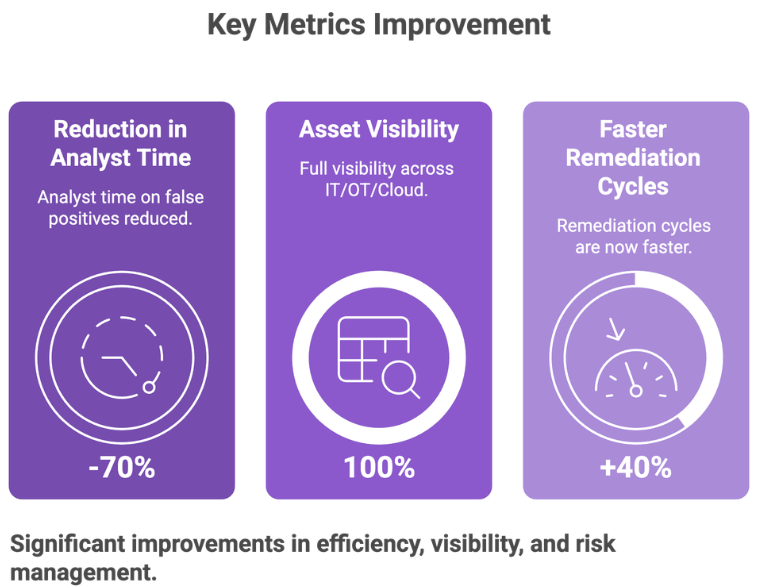
What success looks like
Continuous Threat Exposure Management isn’t a theoretical exercise. It delivers measurable improvements across operational efficiency, risk reduction, and strategic value.
Operational Efficiency
Filter Non-Exploitable Noise
Reduce the volume of vulnerabilities requiring analyst attention by 60-80% by eliminating findings that don’t represent genuine business risk in your specific context. According to [SOURCE NEEDED], the majority of disclosed vulnerabilities are never exploited in the wild—but traditional scanners flag them all as “critical” nonetheless. CTEM helps your team focus on the exposures that actually matter.
Save Labour Hours
Security analysts spend an estimated 30-40% of their time chasing false positives and low-priority findings [SOURCE NEEDED]. By providing contextualised prioritisation, CTEM redirects this effort toward genuine risk reduction and strategic security initiatives.
Increase Remediation Speed
When Security and Operations teams have shared context about why a specific remediation matters, patching cycles accelerate. Clear business justification removes the negotiation overhead that typically delays critical fixes.
Risk Reduction
Quantify Risk Reduction
Move beyond “we patched 1,000 vulnerabilities this month” to “we reduced business-critical exposure by 40% this quarter.” CTEM provides metrics that actually correlate with security outcomes, not just activity.
Achieve 100% Asset Visibility
Discover and inventory all assets across on-premise infrastructure, cloud platforms, and shadow IT. You can’t manage exposure on assets you don’t know exist. CTEM’s continuous asset discovery ensures your inventory reflects reality, not just what’s documented in your CMDB.
Validate Control Effectiveness
Prove your security controls are actually working before attackers test them. Traditional security programs assume that deployed controls are functioning correctly. CTEM validates this assumption and surfaces gaps where controls have degraded, been misconfigured, or never worked as intended.
Strategic Value
Board-Ready Risk Communication
Translate technical security findings into business language that boards and executives can understand and act on. Instead of “we have 5,000 critical CVEs,” explain “we have 12 exposures that could disrupt customer-facing operations, down from 45 last quarter—here’s what we’re doing about them.”
Demonstrate Compliance Readiness
Regulatory frameworks increasingly require evidence of systematic vulnerability management and risk-based prioritisation. APRA CPS 234 for financial services, the SOCI Act for critical infrastructure, and Essential Eight maturity requirements all demand demonstrable security controls. CTEM provides the evidence-based reporting that satisfies these requirements.
Support Investment Decisions
Make data-driven security spending decisions. When you understand which exposures represent genuine business risk and which security controls are (or aren’t) effective, you can allocate budget to initiatives that will achieve measurable risk reduction—not just “best practice” investments of uncertain value.
How CTEM applies across industries
While the fundamental principles of exposure management are universal, the specific applications and priorities vary significantly by industry. Here’s how leading organisations in different sectors are approaching CTEM:
 Financial Services
Financial Services
“Where regulatory scrutiny meets operational complexity”
Australian financial institutions face intensive oversight from APRA, increasingly sophisticated cyber threats targeting payment systems and customer data, and zero tolerance for operational disruption during critical business periods.
CTEM helps financial services organisations: – Demonstrate cyber resilience to regulators through evidence-based risk reporting – Prove systematic third-party risk management across payment networks and service providers – Quantify risk reduction for board-level reporting and regulatory submissions – Manage exposure across complex hybrid environments—trading platforms, core banking systems, customer portals, and cloud-based innovation initiatives – Prioritise remediation during high-risk periods (end of financial year, regulatory audits) without disrupting business operations
 Critical Infrastructure & Utilities
Critical Infrastructure & Utilities
“Where exposure has physical consequences”
For organisations managing operational technology—energy generation and distribution, water treatment, transportation systems—cyber exposure isn’t just about data theft. It’s about operational continuity and physical safety.
CTEM helps critical infrastructure organisations: – Achieve IT/OT convergence visibility—understanding exposure across both corporate networks and industrial control systems – Demonstrate SOCI Act compliance readiness through systematic exposure management – Maintain operational resilience for essential services that Australians depend on – Discover shadow IT and forgotten assets in complex industrial environments where equipment lifecycles span decades – Prioritise remediations that could impact safety-critical systems differently from corporate IT
Orro’s unique capability in this space: Our OT SOC expertise means we understand exposure management where cyber risk has physical consequences—something most MSSPs simply can’t address.
 Healthcare
Healthcare
“Where patient safety depends on system availability”
Healthcare organisations manage Protected Health Information (PHI) subject to Privacy Act requirements, operate clinical systems where downtime directly impacts patient care, and increasingly rely on connected medical devices with embedded vulnerabilities.
CTEM helps healthcare organisations: – Prioritise exposures based on patient safety impact, not just data sensitivity – Manage vulnerability remediation in medical devices and clinical systems where patching requires vendor coordination and complex testing – Demonstrate Privacy Act compliance through systematic data protection measures – Balance security remediation against the operational imperative of continuous patient care availability – Address the unique challenge of legacy systems that can’t be easily upgraded but remain critical to operations
 Government & Public Sector
Government & Public Sector
“Where public trust requires demonstrable security”
Government entities face intense scrutiny of their cybersecurity practices, must demonstrate compliance with the ISM and Essential Eight frameworks, and manage the challenge of serving the public while protecting sensitive citizen data.
CTEM helps government organisations: – Achieve and demonstrate Essential Eight maturity through evidence-based control validation – Align with whole-of-government security frameworks and shared service models – Provide transparency in risk management for ministerial briefings and public accountability – Protect citizen data across increasingly digital service delivery channels – Manage exposure across complex federated IT environments with multiple agencies and shared services
 Retail
Retail
“Where downtime directly impacts revenue”
Retail organisations operate on thin margins where every hour of point-of-sale downtime translates directly to lost revenue, manage complex supply chain systems with numerous integration points, and face intense pressure during peak trading periods.
CTEM helps retail organisations: – Prioritise exposures in payment systems and point-of-sale infrastructure that directly impact revenue – Manage supply chain and logistics system vulnerabilities that could disrupt operations – Ensure operational resilience during peak seasons (Black Friday, Christmas, end of financial year sales) – Protect customer payment data and personal information across digital and physical retail channels – Balance security remediation against the operational reality of 24/7 retail operations
Is exposure management right for you?
CTEM delivers significant value for organisations with sufficient complexity and risk exposure to justify continuous management. Here’s how to assess fit:
You’re a Strong Fit for CTEM If:
✓ You have 200+ assets across on-premise, cloud, and hybrid environments—enough complexity that manual prioritisation breaks down
✓ Your security team is overwhelmed by “critical” vulnerability alerts with no clear way to prioritise remediation efforts
✓ IT Operations and Security struggle to agree on remediation priorities because there’s no shared context about business impact
✓ You need to demonstrate cyber resilience to your board, regulators (APRA, SOCI Act), cyber insurers, or major customers
✓ You’re in financial services, healthcare, critical infrastructure, or government—sectors where cyber risk has significant business or operational consequences
✓ You already have vulnerability management tools but lack the context layer to make them useful for decision-making
✓ You’re mature enough to have shadow IT blind spots you’re worried about—cloud instances, SaaS applications, or OT systems not in your inventory
✓ You’re looking for continuous management, not point-in-time assessments—you understand that exposure changes as your environment evolves
You’re Not Yet Ready If:
⊘ You have fewer than 50 assets or a very simple IT environment—the overhead of CTEM likely exceeds the value
⊘ You don’t yet have basic vulnerability scanning in place—get foundational controls established first
⊘ Your primary concern is compliance checkbox exercises, not real risk reduction—CTEM is overkill for simple compliance documentation
⊘ You’re looking for a one-time assessment rather than continuous management—a traditional penetration test or security assessment may be more appropriate
⊘ You don’t have organisational readiness to act on findings—CTEM generates actionable intelligence, but that intelligence requires follow-through
The honest truth: CTEM is a strategic security investment for organisations facing genuine complexity. If you’re uncertain whether you need this level of sophistication, a complimentary discussion with our team can help assess fit.
Where exposure has physical consequences
Most CTEM conversations focus exclusively on IT environments—servers, cloud platforms, applications, and corporate networks. But for organisations managing operational technology, cyber exposure doesn’t just threaten data. It threatens operations, safety, and physical assets.
The IT/OT Exposure Challenge
Operational technology environments—manufacturing systems, building management, energy distribution, water treatment, transportation infrastructure—were historically isolated from corporate IT networks. This “air gap” was the primary security control.
That air gap no longer exists in most organisations.
Modern industrial environments increasingly depend on IT/OT convergence: – Remote monitoring and diagnostics requiring internet connectivity – Cloud-based analytics on operational data – Shared identity and access management systems – Supply chain integration connecting OT networks to partners – Corporate IT systems managing OT environments
This convergence creates exposure that traditional IT-focused security programs don’t address:
Legacy Systems with Decades-Long Lifecycles
Industrial control systems and SCADA equipment often run for 20-30 years. They were designed before cybersecurity was a consideration. They can’t be easily patched or upgraded. But they’re increasingly network-connected, creating exposure that can’t be remediated through traditional vulnerability management.
Safety-Critical Systems Where Availability is Paramount
In OT environments, the security principle of “confidentiality, integrity, availability” inverts to “availability, integrity, confidentiality.” Taking a water treatment system offline to patch a vulnerability isn’t acceptable if it disrupts essential services. This requires fundamentally different risk prioritisation.
Physical Consequences of Cyber Incidents
A cyber incident in an IT environment might result in data theft or business disruption. The same incident in an OT environment could result in physical damage to equipment, environmental incidents, or safety risks to personnel. The risk calculation is fundamentally different.
Orro’s IT/OT CTEM Capability
Orro is one of the few providers in Australia who can deliver exposure management across both IT and OT environments. This capability builds on our OT SOC expertise—we don’t just understand IT security; we understand the operational realities of industrial environments.
For organisations managing operational technology, our CTEM service provides:
Unified Visibility
A single exposure view across corporate IT networks and operational technology environments—understanding how vulnerabilities in IT systems could impact OT operations and vice versa.
OT-Appropriate Risk Prioritisation
Context-based prioritisation that factors in operational requirements, safety considerations, and the reality that many OT systems can’t be patched on a normal IT timeline.
IT/OT Attack Path Validation
Understanding whether exposure in corporate IT networks could enable lateral movement into OT environments—and whether existing segmentation controls are actually preventing this.
Safety-Conscious Remediation Planning
Remediation strategies that respect operational constraints—scheduled maintenance windows, safety protocols, and the reality that availability often trumps immediate patching in industrial environments.
This IT/OT convergence capability is particularly valuable for: – Critical infrastructure and utilities (energy, water, transportation) – Manufacturing and industrial operations – Building management and facilities (large campuses, data centres) – Healthcare (clinical systems, medical devices) – Any organisation where cyber exposure could impact physical operations
If your organisation manages operational technology alongside corporate IT, exposure management needs to reflect this reality—not just treat everything as if it were a corporate server.
Designed to meet you where you are
Every organisation’s exposure management journey is different. Some are ready for comprehensive managed services with full platform deployment. Others need to start with a diagnostic assessment to understand their current state before committing to ongoing management.
Orro offers flexible engagement models designed to match your current maturity, environment complexity, and risk priorities:
For organisations just beginning to think about exposure management, we can start with lightweight integration of your existing tools—consolidating vulnerability data from Qualys, Tenable, or Microsoft Defender into a unified risk view without requiring infrastructure deployment. This provides immediate value through better prioritisation while you assess whether continuous management makes sense for your organisation.
For organisations ready to mature their vulnerability management program, we can deploy comprehensive scanning and monitoring across hybrid environments—on-premise infrastructure, cloud platforms, identity systems—with full contextual analysis and continuous remediation guidance.
For organisations requiring full exposure command capabilities, we can implement cloud security posture management, identity risk analysis, and advanced threat validation alongside traditional vulnerability management—creating a complete picture of exposure across every dimension of your environment.
The specific approach depends on factors like: – Current security tool investments and whether they can be leveraged – Environment complexity (number of assets, cloud vs on-premise, IT/OT mix) – Internal security team capacity and where you need augmentation vs full managed services – Regulatory requirements and whether you need specific compliance reporting – Risk tolerance and how aggressively you need to reduce exposure
In a complimentary discussion, we’ll explore your specific situation and recommend the right path forward—no sales pitch, just strategic guidance on whether CTEM makes sense for your organisation right now, and if so, how to approach it in a way that delivers value without overwhelming your team.
This consultative approach is important because CTEM isn’t right for every organisation, and even when it is right, the implementation path should be tailored to your reality—not a one-size-fits-all package.
Understand your exposure landscape
If you’ve read this far, you’re likely dealing with the challenges CTEM is designed to solve: too much vulnerability data, not enough clarity about what actually threatens your business.
We offer two ways to explore whether exposure management makes sense for your organisation:
Path A: Cyber Governance Maturity Assessment
Not sure where you stand?
Complete a free cyber governance maturity assessment to understand your current security posture across five key capability areas: Identify & Govern, Protect, Detect, Respond, and Recover & Improve.
In 10 minutes, you’ll receive: – Your maturity score benchmarked against similar organisations – Identification of critical gaps in your security program – Personalised recommendations for improvement – A foundation for prioritising security investments
This assessment helps you understand whether your organisation has the foundational security controls in place to benefit from CTEM, or whether you need to address more fundamental gaps first.
Path B: CTEM Consultation
Ready to discuss your exposure landscape?
Request a complimentary 30-minute consultation with our exposure management team to explore how CTEM could work in your specific environment.
We’ll discuss: – Your current vulnerability management challenges and pain points – How CTEM could address these challenges in your specific context – Whether your organisation is ready for continuous exposure management or needs intermediate steps – What a phased implementation might look like given your constraints – Honest assessment of whether this investment makes sense for you right now
This isn’t a sales pitch. It’s a strategic conversation to help you understand your options. If CTEM isn’t the right fit for your organisation at this stage, we’ll tell you—and suggest what might make sense instead.
Why Orro for Exposure Management?
Nearly 30 years of Australian cybersecurity expertise
National Cyber Defence Centre monitoring millions of events daily
Direct Rapid7 partnership with platform expertise across 100+ security tools
IT/OT convergence capability for organisations where exposure has physical consequences
Strategic consulting approach that goes beyond tool deployment to deliver security outcomes
Trusted by organisations across financial services, government, healthcare, and critical infrastructure to protect what matters most.
Frequently Asked Questions
Do we need to replace our existing vulnerability management tools?
No. CTEM works with your existing security investments—Qualys, Tenable, Rapid7, SentinelOne, CrowdStrike, and 100+ other platforms. We integrate data from your current tools to provide the missing context layer, not replace what’s working. Many of our clients already have vulnerability scanning in place; they come to us because they need help making sense of what those scanners are telling them.
How is this different from what our SOC already does?
Your Security Operations Centre focuses on detecting and responding to active threats and security incidents—monitoring for suspicious behaviour, investigating alerts, and containing breaches. CTEM focuses on identifying and prioritising exposures before they become incidents—understanding which vulnerabilities could be exploited and need remediation. Think of them as complementary capabilities: CTEM tells you what to fix before it’s exploited, your SOC detects and responds when prevention fails. Organisations operating both capabilities see the greatest risk reduction.
What’s the difference between CTEM and a traditional vulnerability assessment?
Traditional vulnerability assessments are point-in-time snapshots that generate long lists of findings with limited business context. You get a PDF report with hundreds or thousands of vulnerabilities, all flagged as “high” or “critical,” with minimal guidance on what to prioritise. CTEM is continuous monitoring with business context, threat intelligence, and control validation—providing ongoing prioritised guidance that evolves as your environment changes and new threats emerge. It’s the difference between an annual medical exam and ongoing health management with real-time coaching.
How long does it take to see value from CTEM?
Most organisations see immediate value in the first 30 days through reduced alert noise, clearer remediation priorities, and actionable guidance that Security and Operations teams can align on. The strategic value compounds over time as you track risk reduction trends, validate control effectiveness, and make data-driven security investment decisions. Early adopters typically report that CTEM “pays for itself” within the first quarter through more efficient use of existing security team time.
What if we’re not ready for a full CTEM program?
That’s perfectly fine, and in many cases, the honest answer. We offer flexible engagement models, including lightweight options that integrate with your existing tools without requiring infrastructure deployment or long-term commitments. A complimentary consultation will help determine what makes sense for your current state—whether that’s full managed CTEM, a phased approach starting with specific high-risk environments, or foundational work on asset inventory and control validation before advancing to continuous exposure management.
Is this only for large enterprises?
CTEM delivers value for any organisation with 200+ assets across on-premise and cloud environments, regardless of total company size. We work with mid-market organisations and enterprises alike. The key indicators are environment complexity and the degree of pain your team is experiencing with current vulnerability management approaches—not company size or revenue. A 300-person financial services firm with complex hybrid infrastructure may benefit more from CTEM than a 5,000-person organisation with simple, homogeneous IT.
How does Orro’s CTEM service handle operational technology (OT) environments?
Unlike most CTEM providers who focus exclusively on corporate IT, Orro extends exposure management across both IT and OT environments. This is particularly valuable for critical infrastructure, manufacturing, utilities, and any organisation where cyber risk has physical consequences. Our OT SOC capability means we understand the unique constraints of industrial environments—decades-long equipment lifecycles, safety-critical systems where availability is paramount, and the reality that traditional patching approaches don’t work in OT contexts. We provide unified visibility across IT/OT while respecting the operational realities of each domain.
What does “context over severity” actually mean in practice?
It means we don’t rely solely on CVSS scores to determine remediation priority. Instead, we factor in where the vulnerable asset sits in your network (internet-facing vs internal), what it’s used for (production customer database vs test environment), what data it processes (sensitive customer information vs non-sensitive test data), whether there are compensating controls (WAF protecting the application, network segmentation limiting lateral movement), and whether the vulnerability is being actively exploited in the wild. This contextual analysis means a CVSS 9.8 on a low-value asset can be appropriately deprioritised, while a CVSS 6.5 on a critical business system with no controls moves to the top of the queue. It’s risk-based prioritisation, not score-based triage.
How do you validate that our security controls are actually working?
We test attack paths to confirm that your deployed security controls are functioning as intended. For example, if you have a Web Application Firewall protecting internet-facing applications, we validate whether it’s actually blocking the attack categories it should prevent—not just assume it’s working because it’s deployed. If you have network segmentation policies intended to prevent lateral movement from corporate IT to sensitive data environments, we test whether those policies are properly configured and enforced. This control validation often surfaces gaps where controls have degraded over time, been misconfigured during deployment, or never worked as documented—providing opportunities to remediate before attackers test the same paths.
Ready to Take the Next Steps?
Whether you’re assessing readiness, planning a modernisation program or simply exploring what AI-Native Networking could mean for your environment — our team can help build a roadmap grounded in evidence, not assumptions.
Speak with an Orro Cyber Specialist